– By Lalit Choda (Mr. NHI)
The cybersecurity perimeter isn’t just about human users or login screens anymore. Instead, it’s moving toward something a lot more complex and maybe even more risky: Non-Human Identities (NHIs) that act on their own, make choices, and have control over various systems.
These days, there are way more NHIs than human identities, with LLM agents and software supply chain bots leading the pack—it’s a ratio of 25 to 50 times! But as these digital entities keep growing, there’s a big gap in how we manage them. We’ve got the hang of authenticating users. We still haven’t figured out how to manage machines that can think and act on their own.
So, this is where the Model Context Protocol (MCP) steps in. MCP isn’t just a buzzword; it’s an up-and-coming protocol designed to provide digital entities with a structured behavioral context. It suggests moving away from identity-based access to a system that enforces execution based on context, tying what a machine can do to the where, when, and why of its actions.
What Exactly Is Model Context Protocol?
The Model Context Protocol, or MCP, is a structured and open protocol that aims to link large language models (LLMs) with tools, data, and services in a standardized and secure manner.
When an AI model like Anthropic’s Claude or OpenAI’s GPT needs to do things beyond what it knows—like checking a database, calling a REST API, or getting private data—it can use MCP to ask for access and get a response from a trusted server.
But MCP is more than just connections. It gives you the lowdown on what’s happening: what the model is up to, what tools it can use, who the user is, what data is being accessed, and the policy guiding the action.
MCP makes sure every decision or action taken by an NHI includes:
- The intended behavior and model state
- The policy scope (what’s allowed and what’s not)
- The source of invocation (who or what triggered the action)
- The environmental metadata (time, workload type, data boundaries)
MCP vs Traditional IAM: What’s New?
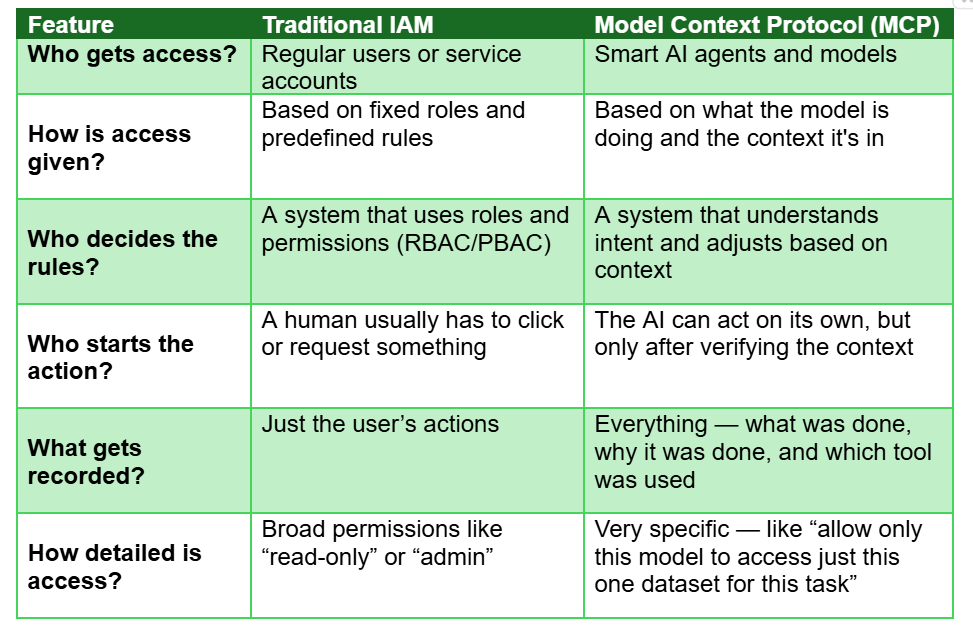
MCP = Identity + Execution Context + Behavioral Constraints.
MCP takes things a step further than traditional IAM systems. While those systems focus on identifying who an entity is, MCP asks, “Should this action be allowed right now, in this context, and with this level of trust?”
How MCP and NHIs Intersect
AI models that interact with systems, like retrieving sensitive records, are effectively acting as NHIs. That means they must be:
- Identified: Who or what is the agent?
- Scoped: What can it do?
- Monitored: What has it done?
MCP provides the structure for these controls. It allows organizations to delegate actions to AI agents safely, while enforcing security boundaries and business logic around what those agents can see or do.
Through MCP:
- NHIs powered by LLMs can access tools only when explicitly allowed
- Context (user session, role, task) is embedded with every action
- Organizations retain full control over tool servers, data policies, and logging
The NHI Problem
Back in the day, identity was just about having a username and password. For NHIs, identity feels a bit abstract. These Non-Human Identities (NHIs) have become the main players in many organizations, actually outnumbering human users by a significant margin. You’ve got service accounts, API keys, LLM models, and AI agents in the mix.
What’s the issue? So, these NHIs are:
- Invisible, since they’re not really monitored like human users
- Powerful because they have broad permissions
- Poorly governed, often having stale credentials or no clear owner
MCP shifts the discussion from “what identity is this?” to “what context is this action happening in?” That shift really changes the game.
MCP’s Approach to Tackling NHI Issues
The Model Context Protocol (MCP) secures NHIs by incorporating context, control, and traceability into each action they take:
- Contextual Execution – MCP ensures that an NHI can only work within its intended model scope. For example, an AI agent trained for documentation cannot suddenly interact with financial systems.
- Policy Binding – Rather than just linking access rules to an identity, MCP applies behavioral policies at the model context level. NHIs are guided by their identity, actions, and the reasons behind them.
- Auditability – Every action taken by an NHI through MCP is logged with full context: intent, origin, scope, and response. This enables accountability, trust, and compliance.
Challenges
Every transformation comes with its challenges. To adopt MCP, we need to tackle:
- Context Modelling – Defining accurate boundaries for complex systems can be tough, especially in multi-agent or hybrid cloud environments.
- Legacy Compatibility – Many IAM systems weren’t built to handle contextual enforcement. Integrating MCP requires effort.
- Standardization – For MCP to succeed, it must work across platforms. Without common schemas and tool servers, fragmentation risks undermining its potential.
The Future of MCP
For a secure future with NHIs, we can’t just depend on old-school human access controls. As machines get smarter and start making decisions, the way we govern them must adapt too.
The Model Context Protocol provides a way to move ahead. It’s not a quick fix, but it marks a shift from fixed identities and wide-ranging permissions to flexible, context-based policy enforcement. If designed well, MCP could make NHIs predictable, safe, and accountable.
The future of cybersecurity is moving away from just usernames and passwords. It’s going to be influenced by the model’s identity, the scope of the task, and the limits on behavior. MCP is set to be a key building block for Zero Trust in machine-driven infrastructure. When it comes to AI assistants handling workflows or robotic process automation in finance, it’s all about earning trust through actions rather than just relying on credentials.